Juliano Rizzo and security experts Alex Rad state to get found major flaws within the Telegram secure messaging application, primarily related to the “visual fingerprint” that correspondents should use to guarantee the protection of a finish-to-end encrypted conversation.
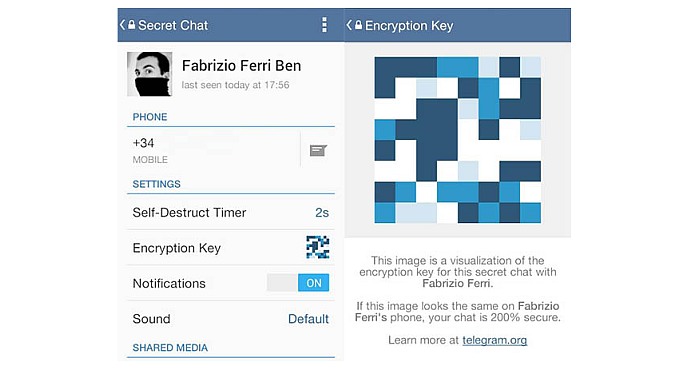
Telegram talks aren’t stop-to-end safe automatically, so when customers wish to put up a completely protected talk they have to evaluate these visible fingerprints — based on the shared secret key for that discussion – to check on they discover the same, therefore the shared key hasn’t been tampered with.
Telegram replied on Facebook to state they got their numbers wrong, which could be really expensive…
Rad and Rizzo also criticized Telegram for using SMS like a user authentication system, as “SMS could be sniffed and damaged, goals could be attached to fake base stations, and companies could be compromised.” this could clearly also influence those using MMS systems to evaluate visual fingerprints.
The scientists named on Telegram to create all talks stop-to-end encoded automagically, change from per-talk certification to correct public key cryptography (as utilized by the kind of OTR, Threema and TextSecure), and expose a brand new user authentication system.
To respect privacy, Telegram should allow communications decoupled in the requirement of a telephone number along with address books to ensure that people may use Telegram anonymously, that is currently impossible,” they added.
Berlin-based Telegram sent me a declaration in reaction to your blog post, observing in reaction to the “super villain” assault concept that – along with the $1 billion problem – “people often contact help if your key talk requires greater than a few moments to be produced – and below it’d need to take 30 days”